|
|
Post by nodstar on Jun 12, 2009 17:05:55 GMT 4
This thread is for helpful computer advice ... Please feel free to post your helpful computer tips here  |
|
|
|
Post by towhom on Jun 12, 2009 21:50:50 GMT 4
Google plugs 'high risk' WebKit holes in ChromeZDNet News & Blogs / Technology News
Posted by Ryan Naraine
June 11th, 2009 @ 7:50 amblogs.zdnet.com/security/?p=3585&tag=nl.e589Google has shipped a Chrome browser update to fix two serious security issues in WebKit. According to Google Chrome program manager Mark Larson, the most serious of the two flaws could allow hackers to execute harmful code in the browser’s sandbox. It is rated “high severity.” From Google’s advisory: A memory corruption issue exists in WebKit’s handling of recursion in certain DOM event handlers. Visiting a maliciously crafted website may lead to a tab crash or arbitrary code execution in the Google Chrome sandbox. This update addresses the issue through improved memory management. [ SEE: Study: Silent patching best for securing browsers ] For an attack to be successful, the victim would havve to visit a Web page under the attacker’s control. Larson said that any code that an attacker might be able to run inside the renderer process would be inside the sandbox. The update also fixes: An issue exists in WebKit’s handling of drag events. This may lead to the disclosure of sensitive information when content is dragged over a maliciously crafted web page. This update addresses the issue through improved handling of drag events. Google rates this a “medium” severity bug and warns that an attacker might be able to read data belonging to another web site, if a user can be convinced to select and drag data on an attacker-controlled site. The patch is being pushed out to Google Chrome via the browser’s silent/automatic update mechanism. The above is additional information related to 2 previous posts:
See Rule 3: Run suspicious programs in a sandbox
the-goldenthread.proboards.com/index.cgi?board=general&action=display&thread=2&page=135#2828
Use a sandbox to improve your PC security
the-goldenthread.proboards.com/index.cgi?board=general&action=display&thread=2&page=135#2829
The Sandboxie program is for PCs (only). Google Chrome, however, is available for MAC and Linux. I was waiting for the above critical issue resolution (uh huh - one problem down, one trillion to go...) on the embedded sandbox feature before posting this option.
See this link to download Google Chrome for MAC and Linux along with a (preliminary) software review. If you already are using Google Chrome and its embedded sandbox feature, it appears that the update will be automatically (silently) done (since I'm not a Google fan, I don't have this browser).
I will admit, having read all of the documentation via the links in the article and the additional links available via the review, this browser is still in a beta stage for MAC and Linux (although "they're working on it"). In addition, the developer version is pretty "heavy" - most would download the "stable" version (isn't that an oxymoron - "stable" but "beta"?). I can't even state that the "update" will be applied to the MAC and Linux versions.
Please keep this in mind.
Hope this helps.
Sally Anne
|
|
|
|
Post by towhom on Jun 13, 2009 2:27:16 GMT 4
Use a sandbox to improve your PC securityWindows Secrets
By Ian "Gizmo" Richards
Best Software, October 16, 2008 Sandboxes are a relatively new type of security product that can significantly reduce your chance of getting infected when you surf or when you download and install programs. I'll explain why sandboxes are so important and show you how to use my favorite sandbox program. Block access to system files as you browse A security sandbox is a program that creates an isolated environment on your PC within which other programs can run. It sets up a kind of virtual PC within your real PC. Programs running in that virtual PC are corralled from the rest of the system. It's like building a room in the deep interior of your house with no windows or doors. What takes place in that room cannot affect what takes place in the rest of your house. In the same way, what takes place in a security sandbox cannot affect your PC. Now, this may sound abstract and theoretical, but it has some very practical implications. First, if you run an infected program within the sandbox, the infection is restricted to the sandbox and cannot get to your real PC. Second, when you shut down the sandbox, the infection is eliminated from your PC. It will be gone forever without ever affecting your system. These characteristics make sandboxes ideal for improving your PC's security. And, as we shall see in the next section, sandboxes address the latest type of security threat confronting PC users: hostile Web sites. Why sandboxes are important to your security A few years ago, the major risk PC users faced was getting infected by a virus or worm that was contained within an e-mail. You may recall a time when there seemed to be a major virus outbreak every few weeks. Not anymore; with improved ISP e-mail filtering and more extensive use of antivirus products, large-scale, e-mail–borne virus outbreaks have become uncommon. They're not eliminated but are much less frequent. Today, there is a new threat: infection by visiting a hostile Web site. It works like this: You go to a seemingly innocent site. While you are viewing the site in your browser, your PC has been silently probed for security vulnerabilities by malware implanted surreptitiously in the site. Once the malware finds a weakness, the site secretly downloads Trojans, keyloggers, and other malicious software onto your PC. You are not even aware of what has happened. What does this secretly downloaded malware do? Pretty well anything the criminals behind the scheme want it to. For example, they could take control of your PC and turn it into a remote-controlled slave PC — or zombie — that will do its master's bidding. This may be sending out spam e-mail, attacking Web sites targeted for extortion, or engaging in numerous other criminal and fraudulent activities. Alternatively, the criminals may install a keylogger on your PC that transmits details of your banking and financial details to some remote computer. Standard PC security measures aren't enough At this stage, many of you are probably thinking, "This can't happen to me. I visit only reputable Web sites. Besides, my PC has all the latest Windows security updates installed and I have an excellent antivirus program." While good security practices will certainly reduce your chances of being infected by a hostile Web site, you can still get infected. Furthermore, the risk is greater than you may think. Here's why: First, an increasing number of hostile Web attacks are from reputable sites. Criminals may take control of a legitimate Web site via security vulnerabilities in the site's software. They can then use the site to infect unsuspecting visitors. It may be hours or days before the site owners detect and correct the problem. In the meantime, thousands of unsuspecting visitors to the site could be infected. The most famous example of this process was the Super Bowl incident last year. The Web sites of Dolphin Stadium and of the Miami Dolphins football team were hacked and used to distribute a keylogger. The sites were infected for over a week before the problem was discovered. In the interim, thousands of surfers who visited the sites looking for football information instead had their PCs infected. Second, keeping your PC fully up-to-date with the latest Windows security patches may not help, either. Some of these hostile Web attacks use unknown security holes, flaws that even Microsoft doesn't know about. These so-called zero-day vulnerabilities are quite commonly used in hostile site attacks, perhaps because they allow a lot of PCs to become infected in the short time before the site owners discover their site has been hacked. Finally, don't expect your antivirus and antispyware software to fully protect you. Yes, your security software will catch some of these Web-based infections, but the chances of zero-day attacks being detected are not high. Worse still, some of these hostile sites attempt to download software that disables your security software before it gets a chance to warn you of their presence.Now, all this sounds alarming, but keep in mind that the risk that the average user will encounter a hostile Web site is relatively small. There's no need to get into a panic about this; it's just another security risk that all Internet users face. However, though the risk is small, the consequences are serious, so putting some protective measures into place is worthwhile. This is where sandboxing comes into the picture. Using a sandbox for safer browsing My favorite sandboxing program is Sandboxie, which I'll use to illustrate how sandboxes work and how they protect you. Other sandbox programs may work differently. Sandboxie is a small, 350KB program for Windows XP and Server 2003, both 32-bit and 64-bit. The program does not currently work with Windows Vista. Sandboxie is free for personal use, though there is a U.S. $30 registered version with a few more features. Most folks will be happy with the free version, though I encourage you to register if you can afford to, because this program is the work of a single hard-working individual — Ronen Tzur — not a large corporation. After you install Sandboxie, you will notice very little that is different on your PC other than a small, yellow sandbox icon in the system tray. Just because you installed Sandboxie, don't think your browser is now sandboxed. Unlike ZoneAlarm's $30 ForceField and other sandboxing applications, Sandboxie does not set your browser to open in a sandbox automatically. You must do so manually by right-clicking your browser icon and selecting Run sandboxed. Sandboxie can be set up to isolate your browser automatically whenever you open it. To do so, add the name of your browser's executable file, such as firefox.exe or iexplore.exe, to Sandboxie's list of the programs it always opens in a sandbox. I use this setting to ensure that my browser always runs in a sandbox, regardless of whether it is started manually or automatically by clicking a link in a document or e-mail. Some folks like full manual control, while others prefer it to be automatic. With Sandboxie, it's your call. Whatever method you use, Sandboxie employs a simple technique to let you know when your browser is running sandboxed: the program places a number symbol (#) before and after the contents of your browser's title bar. Security apps see in, malware can't see out While running sandboxed, you can browse with near-perfect safety to just about any part of the Web. If you get infected by a hostile site, your antivirus and other security programs can still warn you because they can see into a sandbox, even though sandboxed programs cannot see out. However, be aware that your PC may become infected even if your security programs don't sound the alarm, particularly if you encounter a new zero-day infection. That's no problem when you're using Sandboxie. When you've finished surfing, simply close your browser, right-click the Sandboxie tray icon, and select Terminate programs to remove any program — including malware — that's running in the sandbox. Then select Delete contents to completely remove any downloaded programs. After that, your PC is completely clean, with all traces of infection removed. The same technique can be used to ensure privacy. When you clear the sandbox, all traces of your surfing activity are removed, including the sites you visited, the searches you made, and the files you downloaded. Of course, this can be a mixed blessing: I like to retain my surfing history as well as any saved passwords and bookmarks. But that's no problem: you can set Sandboxie so that programs running in the sandbox have access to certain nominated files outside the sandbox. If you configure Sandboxie to allow sandboxed programs access to your real Favorites folder, then any new bookmarks you create while surfing in the sandbox will be saved. However, you are exposing these shared files to any program running in the sandbox — including malware — so be sensible about what you choose to share. Sandboxing isn't just for Web browsers You can sandbox any program, not just your browser. This is a great way to check out downloadable apps whose integrity cannot be established. Remember what I said earlier: your security software can see into a sandbox even though sandboxed programs cannot see out. Since your antivirus scanner can detect an infected download running in a sandbox, you can simply clear the contents of the sandbox, and all trace of the infection is gone forever. These days, I never surf without a sandbox. On the rare occasions when I get infected, it's a great feeling to simply clear the sandbox contents and know my PC is safe from harm. Sandboxing does not replace your antivirus scanner or other security software. Rather, it provides an additional layer of protection. No individual security solution — including sandboxing — is perfect. The more layers of protection you have, the greater your overall security. I suggest you try the free version of Sandboxie, but first a word of warning: sandboxing programs cause problems on a small percentage of PCs, so before you install Sandboxie or any other sandbox program, please make sure your PC is backed up. That way you can recover in the event of a problem. Please make sure you access and read the "Known Issues" and their solutions BEFORE you install this program. In fact, print the page first so you have the information at hand.
|
|
|
|
Post by towhom on Jun 13, 2009 2:42:31 GMT 4
Prevent your system from becoming infectedWindows Secrets
By Ian "Gizmo" Richards
Best Software, January 15, 2009 What will be the major security risks in 2009? More importantly, what can you do to protect your PC against these risks? Be forewarned: the answers are not quite what you expect. There's more in that download than meets the eye Most PC users have a distorted view of the nature of the security risks they face. Conventional wisdom holds that the three biggest threats come from (1) criminals exploiting flaws in Windows and other software products; (2) e-mail-borne viruses; and, more recently, (3) visits to malicious Web sites. These threats, though real, are relatively minor players: each accounts for only a few percent of home PC infections. No, folks — the biggest threat doesn't come from any of these exotic sources but from something much more common and pedestrian: downloading infected programs. The people who make their living cleaning up infected PCs have known this for years. When they ask users when their problem started, the answer is all too commonly "after I downloaded and installed a new program." Tech-support personnel in corporations will tell you the same thing, and they'll often single out senior managers as particularly susceptible to malware-bearing downloads. This practical experience is borne out in the statistics. Security research company Trend Micro recently reported that of the top 100 infections in the U.S. in 2008, approximately 63% were caused by downloading and running programs. E-mail–borne infections accounted for only 3%, while the exploitation of security flaws in products was responsible for a tiny 1.7% of PC infections. Software thieves get more than they bargained for So, what are these infected programs that users are downloading? They include free games, utilities, toolbars, and just about any other program a malicious site can entice a user into downloading. An even-greater threat are pirated software and pornography. Pirated software is particularly dangerous, because such programs are used widely and are often crawling with viruses. In fact, when I'm looking for a new set of malware for my security tests, I go straight to pirated-software sites and cracked-software sources on BitTorrent. The last time I did this, 39 of the 61 illegal programs I downloaded from BitTorrent were infected. Most of the infections are in the key generators ("keygens"), but in seven of the 39 cases, the infection was in the pirated program itself. Even scarier was how few of these infected downloads had been noted by users in their comments on the BitTorrent search sites. I'm not sure why, though I do know that some malware infections disable your security software, so the commenters were likely unaware of the viruses. I suspect many users of pirated software are smart enough to download a fresh copy of the program from the vendor's site and use only the pirated serial number or keygen they lifted off BitTorrent. Whatever the reason, be assured that you cannot rely on program ratings given by BitTorrent users. Now, all of this sounds very scary, but I don't want to alarm you unnecessarily. Most downloading is perfectly safe. Indeed, downloading and trying new programs is one of the great pleasures of the Internet. However, you do need to be smart about what you download and install. That, as we shall see, is not too hard at all. In the last few years, I've downloaded and installed dozens of programs onto my laptop and it's never been infected by malware. Not even once. This is not due to any technical genius on my part nor to the quality of the security software I use. It's the result of adopting safe downloading practices. If you develop the habit of using these practices, your computer will be just as safe as mine. Rule 1: Download only from reputable sources Following this single rule will cut your risk of infection dramatically. So, what is a "reputable source"? Certainly the following: - Any major download site, such as Download.com, Softpedia.com, and MajorGeeks.com.
- Any site of a reputable developer or vendor, such as Microsoft, Google, HP, and Dell.
- Any open-source software hosted on Sourceforge.net, Mozilla.org, and other large open-source hangouts.
There are, of course, many more "reputable sources." The problem is knowing which sites to trust. McAfee SiteAdvisor is a free plug-in for Internet Explorer ( download page), Firefox ( download page) and MACs ( download page) that rates sites based on a number of security criteria, including whether the downloads from the site are free from malware.  Figure 1. The McAfee SiteAdvisor browser plug-in shows safe (green) and unsafe (red) sites at a glance. Figure 1. The McAfee SiteAdvisor browser plug-in shows safe (green) and unsafe (red) sites at a glance.So, what files are definitely unsafe to download or install? Topping the list are files a site offers to you unprompted or via a popup window. If the site asks whether you'd like to install a toolbar, video viewer, download manager, or whatever, always say no. Such files are the riskiest of all downloads, so never be tempted. Make no exception here; this is seriously dangerous territory. Other unsafe sources are file-sharing services. Never download software from BitTorrent and other file-sharing networks unless you can verify the authenticity and integrity of the download with 100% certainty. For most people, it's best to play it safe and never download from these services. The same prohibition applies to software provided to you by friends and colleagues. Unless it's on the original manufacturer's CDs, there's no way you can verify the authenticity and integrity of the program. Rule 2: Scan all downloaded files Normally, you don't have to worry about scanning files you download, because most of the top antivirus and antispyware programs automatically scan a file when you download it. If you're unsure whether your security product scans downloaded files automatically, you can usually initiate a manual scan by right-clicking the downloaded file and selecting the "Scan this file" option. Unfortunately, even the best AV scanners have a less-than-100% detection rate; a downloaded file may scan as clean yet still be infected. You can further reduce the chance of a file's being infected by making use of a free Web-based scanning service, such as Jotti and Virus Total. These sites run your downloaded file through a dozen or more antivirus and anti-malware programs. Of course, there's still a chance your download is infected, even if it passes all the tests at Jotti or Virus Total. However, the protection these services offer is good enough to keep most PCs safe. Rule 3: Run suspicious programs in a sandbox If you have the slightest doubt about a program or e-mail attachment you downloaded, install the program or open the file in a sandbox or other virtualized environment before you load it on your PC. My favorite sandbox app is the excellent free program called Sandboxie ( download page). This and other virtual environments allow you to install and run programs in an area of your PC that's been specially corralled off. If the program you install happens to be infected, the infection is confined to the sandbox and cannot affect your PC. Any infection can be removed by simply deleting the sandbox or its contents. For more on sandboxes, read my Oct. 16 column. [Note from towhom: I'll post this information later tonight.]A neat feature of sandboxing is that your security software can see what's happening in the sandbox and can warn you of any problem. In fact, it's much easier for your AV scanner to detect an infected program that is actually running than to detect an infection simply by scanning the file before installation. If you install a downloaded program in a sandbox and get no warnings from your security software, it's unlikely that the file is infected. You can then delete the sandbox and install the program with confidence on your real PC. Sandboxes are also great for safely opening e-mail attachments. The next time someone sends you a funny PowerPoint presentation, save the attachment and then open it inside a sandbox. OK, it may take you 20 seconds longer, but that's a lot less time than the hours you'd spend removing a malicious infection from your PC. Rule 4: Read the software licensing agreement Of my four rules for safe downloading, this one is most likely to be ignored. That's a pity, because perusing the end-user licensing agreement (EULA) is a surprisingly good way of determining whether the program you're installing contains any unwanted components. Now, no hacker or Internet criminal is going to tell you in a licensing agreement that they have malicious programs in their software. However, most adware purveyors and spyware vendors will disclose the contents of their "services." That's because adware is quite legal. Indeed, some AV and antispyware programs won't pick up particular adware programs because they're legit. Spend a couple of minutes reading the EULA rather than just automatically clicking the "I have read this and agree" button. If you find reading EULAs too tedious, have Javacool Software's EULAlyzer program read it for you and flag for your attention any worrying paragraphs. EULAlyzer is free for personal and educational use ( more info). In addition to reading the EULA, you should also be vigilant about what you agree to during the program's installation routine. Quite often, software vendors will slip into the install wizard a default selection permitting the installation of a third-party's product, a subscription to their promotional newsletter, or whatever. A common example of this practice is the otherwise excellent freeware disk-cleaning program CCleaner ( more info). Embedded in the utility's install is a default option to add the Yahoo search toolbar to your system. If you don't want the toolbar, you need to uncheck the option. [Note from towhom: I don't allow any other search bar installation, but that's my personal preference. I have enough on my hands tracking on MicroSnot's software and add-ons, so the less I have to follow, the better. Another caution that needs to be stated here - CCleaner, which I use, is an extremely aggressive cleaner. Some may not like the deep cleaning, since some personalized settings may be removed too (like in Access). I'll post some information and other options later.]Now, the Yahoo search toolbar is a legitimate product and quite a good one, in fact. But do you really want it? I don't, and I suspect most other users don't want it, either. The next time you install a program, read before you click. So there you are, folks. Of all the security threats you face, downloading and installing programs is statistically your highest risk. I've outlined four simple rules for downloading that anyone can follow. Just stick to these rules and you're on the way to a malware-free 2009.
|
|
|
|
Post by towhom on Jun 13, 2009 4:37:52 GMT 4
Yes or no to firewall request to act as server? Windows Secrets
By Fred Langa
2009-06-04 It's not always easy to tell whether a program really needs the rights and privileges of a server. When your firewall alerts you that an application wants to act as a server, you have two simple ways to determine the correct response. Find out why a program wants server status Maurice Carson ran into one of those all-too-common, half-explained firewall queries: - "What about programs wanting to 'act as a server'? I have ZoneAlarm as a firewall, and many programs want to act as a server. Why?"
First, let's define the jargon. A "server" is a program that responds to a request from another program to open a connection, send or receive a file or data, launch a program, or perform some other task. A "client" is a program that makes such a request. Technically, client and server programs can reside on the same machine. Security risks come into play when the client and server are on separate networked machines. Some programs are both clients and servers, while others — known as "standalone applications" — are neither. ZoneAlarm and other security tools are especially suspicious of any program that wants to act as a server, because letting other PCs request data or services from your system is obviously risky. The firewall has no way of knowing whether the request to act as a server is legitimate, so it punts the decision to a human — you. The simple, empirical way to respond to a program's request to act as a server is to choose the "No" or "Deny" option (or whatever verbiage your security tool uses) every time. Denying the request is always safest; you'll never reduce your security by blocking a program's request for server rights.Saying no may cause some necessary features or functions of the program to stop working, however. In these cases, the application really does need to act as a server. You can then adjust your security tool's settings accordingly. The "default to No" method is crude but effective. I prefer to figure out why a particular program might need to respond to a client's request for a file or other resource. For example, it's pretty clear that the Skype voice-over-IP (VoIP) tool needs to act as a server in order to respond to incoming phone calls. Likewise, if you use a file-sharing app that makes your PC part of a network for receiving and redistributing files, acting as a server is part of the deal.In cases like these, you'd let the software in question act as a server. But keep in mind that it's always more dangerous to allow server requests. Doing so opens a path into your PC for outside service requests. Of course, this may be necessary for the software to work as intended. If you don't recognize the would-be server program or don't understand why it's making a request to act as a server, do a little research. If possible, query a search engine with the exact wording of the relevant part of your security tool's message, and include the name of the program making the server request. Odds are many other people have asked about the same program and the answer is just a few clicks away. If you can't find an answer online, fall back to the empirical method. Or, as I'd put it more simply: "When in doubt, lock it out, but if it breaks, raise the gates!"
|
|
|
|
Post by towhom on Jun 13, 2009 4:47:38 GMT 4
Why you need to validate your downloads Windows Secrets
By Ian "Gizmo" Richards
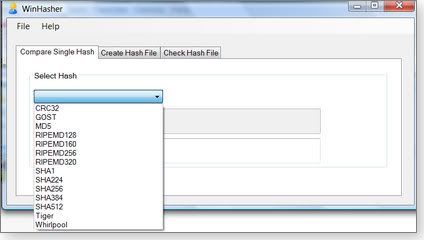
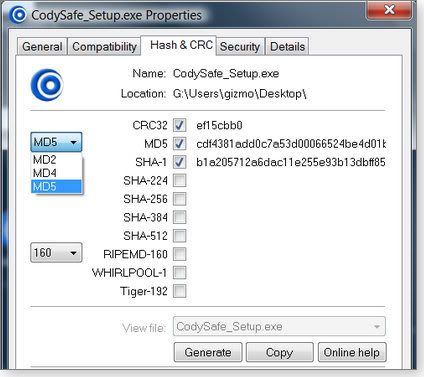
2009-06-04 One of the most common ways of getting a malware infection is by downloading and installing a seemingly legitimate program that has actually been tampered with. You can seriously reduce the risk of this kind of infection by using a free checksum program that makes it easy to validate files before you open them. Using checksums to validate downloadable files The idea of using a checksum calculated from a set of data to validate the accuracy of that data is not restricted to file downloading; it is commonplace. Take, for example, your credit card. Whenever you give someone your credit card number, it's important that they get it exactly right. However, there's always a chance that you or the person recording your card number will make a mistake. To guard against these transcription errors, credit card companies have built in a simple checking mechanism to ensure the validity of the card number. The last number on your credit card is not part of your account number but is a check digit. If you apply a standard formula to all the other numbers on the card, you should end up with a number corresponding to the check digit. If you don't, something is wrong. An example of such a formula would be to add up all the numbers on the card and then compare the last digit of the result to the check digit. So if your numbers added up to 72, the check digit should be 2. In practice, the formula used for credit cards — called the Luhn algorithm — is a little more complex, but the idea is the same. The Luhn algorithm is just one example of a checksum algorithm. However, it shares a weakness with other simple checksum methods: it can certainly detect incorrect digits but can't detect a lot of other common errors, such as the simple transposition of two digits. To do that, a more complex method is needed. The Cyclic Redundancy Code (CRC) technique is the next step up in error detection. CRC can detect not only incorrect digits but also digits out of sequence. There are many CRC algorithms, but the most common is CRC32. Even CRC32 has a weakness: while it's excellent at detecting accidental errors, it's not robust against deliberate falsification. In other words, it's possible for a knowledgeable attacker to modify the data yet ensure that it generates the correct checksum. To guard against this, we need even more sophisticated methods. These more advanced techniques are usually called cryptographic hashes rather than checksums. The most common of these cryptographic hashes is Message Digest number 5 (MD5), which is capable of producing a 128-bit fingerprint. MD5 is more difficult to falsify by reverse engineering than CRC32. However, even MD5 is no longer considered fully secure. A smart hacker can tamper with the file in such a way that it still gives a valid checksum. MD5 is good enough for casual file verification purposes, but there's a strong move to more-secure hashes, such as the Secure Hash Algorithm (SHA-1) and RACE Integrity Primitives Evaluation Message Digest (RIPEMD, which has evolved into RIPEMD-160 and other, more-recent variants). RACE stands for "R&D in Advanced Communications Technologies in Europe." Ah, we techies do love our embedded acronyms! Whatever the technique, the idea is still much the same as the check digit on a credit card. You run a program that calculates a number — the hash — from the data and compare this to the correct hash quoted for that data by the publisher or download site. If the two don't agree, you have a problem. Why hashes matter when you download a file Just as it's important to get your credit card number right when making a transaction, you need to validate the programs you download before opening them. And believe me, downloads can get corrupted. By far the most common cause is an error in transmission, usually as a result of a download that didn't fully complete. However, even files that appear to download completely can still be corrupted accidentally. But corruption can also be deliberate. A hacker may have modified the original file and secretly inserted a Trojan or other malware program. This is not uncommon for files distributed via BitTorrent or other file-sharing services. (I wrote in my Jan. 15 column that 39 out of 61 illegal programs I tested after downloading them using BitTorrent were infected.) The use of an MD5, SHA-1, or other hash will detect corruption, whether accidental or deliberate. That's why you should validate all downloads against the checksums or hashes provided by the program distributor. Unfortunately, not all download sites provide these hashes, but if they do, be sure to use them. Thankfully, there are some excellent free programs that simplify the task of calculating hashes for your downloaded files. I looked at seven different free checksum and hashing utilities and describe in today's column the three I consider the best for typical PC users. If you want to calculate only the common hashes, such as MD5 or SHA-1, any of these programs will do the job — though they differ in usage and the types of hashes they calculate. #1: WINHASHER 1.03File checker runs from .exe without installer If you download files only occasionally, you may be attracted to WinHasher 1.03, mainly because the program runs directly from the .exe file without installing. However, WinHasher does require the Microsoft .NET Framework 2.0. To use WinHasher, you must first select the hash method you want from a list of eight different hashing algorithms, several of which have iterations of their own. (See Figure 1.) Then you select the file you want to analyze. WinHasher calculates the hash and can also compare it to the hash published by the download site. WinHasher also generates or validates hash files, if required. 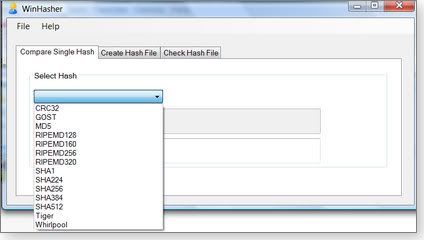 Figure 1. The WinHasher file validator supports eight different hashing algorithms. Figure 1. The WinHasher file validator supports eight different hashing algorithms.The most-recent version, WinHasher 1.4, includes more features, such as the ability to create hashes from the right-click (context) menu and to generate hashes from text. However, this version requires installation. Personally, I prefer the earlier version because it's portable. If you're fine with a program that needs to be installed, however, I suggest you look at either FileTweak or HashCalc, both of which are described below. Download version 1.03 (334KB) from Download.com or version 1.4 (374KB) from the vendor's site. #2: FEBOOTI FILETWEAK HASH & CRC 2.0Check downloaded files via Properties dialog The name "Febooti FileTweak Hash & CRC" might be a mouthful, but this product is delightfully simple to use. Once installed, the program adds a Hash & CRC tab to the file's Properties dialog — the one that opens when you right-click the file and choose Properties. FileTweak handles all the formats shown in Figure 2, plus RIPEMD-128, -256, and -320. However, the program can't compare calculated hashes with published values; you'll need to do that manually. 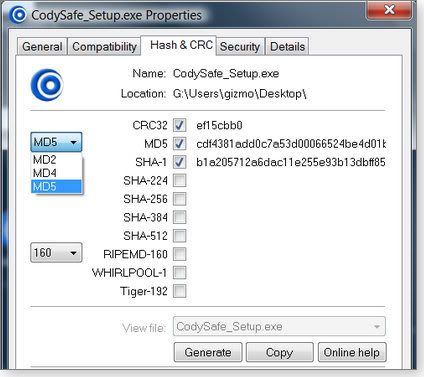 Figure 2. FileTweak adds a file-checker option to the file's Properties dialog in Windows. Figure 2. FileTweak adds a file-checker option to the file's Properties dialog in Windows.Download FileTweak from the vendor's site (264KB). #3: SLAVASOFT HASHCALC 2.02The drag-and-drop way to check your downloadsSlavaSoft's HashCalc runs as a standalone application, so once it's running, you simply select the file you want to check and the hashing method to use, and then click Calculate. Alternatively, you can drag and drop the file into the program window. HashCalc handles 13 different checksum and hashing algorithms, including the special method used by the eDonkey/eMule file-sharing services.  Figure 3. HashCalc supports keyed-Hash Message Authentication Code hashes for an added level of security. Figure 3. HashCalc supports keyed-Hash Message Authentication Code hashes for an added level of security.This program processes not only files but also text or hex strings. It's also the only program of the three described here that can process keyed-Hash Message Authentication Code (HMAC) hashes. HMAC combines a hash with a key and is typically used in high-security environments. HashCalc is available from the SlavaSoft site (468KB). So which is my favorite download verifier? I like WinHasher 1.03 because it's portable and is the only product in this group that checks the generated hash against the published hash. However, the choice is ultimately a matter of personal preference. I suggest you try all three, as they're tiny programs that can be downloaded in a few seconds. But please do get yourself a hash-checking program. There are simply too many dodgy downloads floating around the Internet to risk accidentally downloading a file that has been tampered with. Make sure, though, to get your published hashes or checksums from the original source of the program rather than get some untrustworthy value obtained from a file-sharing service.
|
|
|
|
Post by towhom on Jun 13, 2009 4:58:17 GMT 4
I, myself, am not a fan of QuickTime - however - here is (are) the fix(es) for the latest wormy Apple stuff...I'm still waiting for the latest DirectX patches from MicroSnot... Apple plugs gaping QuickTime security holesZDNet News & Blogs / Technology News
by Ryan Naraine
Posted: June 1st, 2009 @ 1:37 pmblogs.zdnet.com/security/?p=3479&tag=nl.e550Apple today released QuickTime 7.6.2 with fixes for a variety of security vulnerabilities, some of which could lead to arbitrary code execution attacks. The update, available for Mac OS X, Windows XP and Windows Vista, covers a total of 10 documented vulnerabilities that could be exploited via booby-trapped movie, video, image and audio files. Here are the details: - CVE-2009-0188: A memory corruption issue exists in QuickTime’s handling of Sorenson 3 video files. This may lead to an unexpected application termination or arbitrary code execution.
- CVE-2009-0951: A heap buffer overflow exists in the handling of FLC compression files. Opening a maliciously crafted FLC compression file may lead to an unexpected application termination or arbitrary code execution.
- CVE-2009-0952: A buffer overflow may occur while processing a compressed PSD image. Opening a maliciously crafted compressed PSD file may lead to an unexpected application termination or arbitrary code execution.
- CVE-2009-0010: An integer underflow in QuickTime’s handling of PICT may result in a heap buffer overflow. Opening a maliciously crafted PICT file may lead to an unexpected application termination or arbitrary code execution.
- CVE-2009-0953: A heap buffer overflow exists in QuickTime’s handling of PICT images. Opening a maliciously crafted PICT file may lead to an unexpected application termination or arbitrary code execution.
- CVE-2009-0954: A heap buffer overflow exists in QuickTime’s handling of Clipping Region (CRGN) atom types in a movie file. Opening a maliciously crafted movie file may lead to an unexpected application termination or arbitrary code execution.
- CVE-2009-0185: A heap buffer overflow exists in the handling of MS ADPCM encoded audio data. Viewing a maliciously crafted movie file may lead to an unexpected application termination or arbitrary code execution.
- CVE-2009-0955: A sign extension issue exists in QuickTime’s handling of image description atoms. Opening a maliciously crafted Apple video file may lead to an unexpected application termination or arbitrary code execution.
- CVE-2009-0956: An uninitialized memory access issue exists in QuickTime’s handling of movie files. Viewing a movie file with a zero user data atom size may lead to an unexpected application termination or arbitrary code execution.
- CVE-2009-0957: A heap buffer overflow exists in QuickTime’s handling of JP2 images. Viewing a maliciously crafted JP2 image may lead to an unexpected application termination or arbitrary code execution.
The update is available via the Software Update utility (Mac OS X) and Apple’s Windows Automatic Software Update tool (Windows). Alternatively, QuickTime 7.6.2 may be obtained from the QuickTime Downloads site.
|
|
|
|
Post by towhom on Jun 13, 2009 5:14:59 GMT 4
Microsoft sneaks in Firefox extension via UpdateZDNet News & Blogs / Community
by Joe Brockmeier
Posted: May 31st, 2009 @ 6:42 pmblogs.zdnet.com/community/?p=293The good news is that Microsoft is writing extensions for Firefox. The bad news is, the Redmond giant is slipping the extension onto systems without notifying users and making it difficult to get rid of the extension. Even worse? It’s an extension that allows Web sites to install software onto users’ PCs behind the scenes — meaning that Firefox users on Windows may not be as safe as they think.Brian Krebs, who originally recommended the .Net Framework that sneaks the extension into Firefox writes: Anyway, I’m sure it’s not the end of the world, but it’s probably infuriating to many readers nonetheless. Firstly — to my readers — I apologize for overlooking this…”feature” of the .NET Framework security update. Secondly — to Microsoft — this is a great example of how not to convince people to trust your security updates. Krebs is right: It’s not the end of the world. But it seems like a violation of user trust to monkey with a third-party program — and top it off by making it difficult to remove the extension without editing the Windows Registry. By using the update mechanism to sneak software onto the system, Microsoft is telling security conscious users to be suspicious of updates and to deploy them only after they’ve been widely vetted, or choose a more trustworthy vendor. As a Linux user, it makes little difference to me what Microsoft does via Windows Update –users on openSUSE and other Linux distros can see exactly what updates will do to their system: Down to the source code, if they choose to take the time. But, failing a source code audit, Microsoft could at least provide a full disclosure of the packages and features modified when a user runs Windows Update. Without that, users should be wary indeed of trusting Microsoft’s updates — and missing a trust relationship for security updates, users should be wary of running Windows in the first place.
|
|
|
|
Post by towhom on Jun 13, 2009 5:21:46 GMT 4
Supreme Court to hear patent case with broad implicationsZDNet News & Blogs / Government
Posted by Richard Koman
June 1, 2009 @ 9:44 AMgovernment.zdnet.com/?p=4875Weather-based risk in commodities trading. Is that too abstract for a patent? Maybe not. While the question may seem arcane, it actually has big import for high-tech. The Court of Appeals for the Federal Circuit rejected the patent on the so-called business method patent because it was too abstract. The inventors say the invention is patentable because “it produced a useful, real-world result: the ability to buy or sell commodities over a given time period at fixed prices,” according to the Wall Street Journal. The case pits biotech against high-tech again, the Journal says, as it’s another attempt to broaden patent protections. International Business Machines Corp., Dell Inc. and Microsoft Corp. were among the companies who had urged the lower court to rein in patent rights, while biotechnology groups warned that changes to current patent standards could harm patent protections for biotech inventions. POTUS to SCOTUS: Leave Cablevision decision aloneZDNet News & Blogs / Government
Posted by Richard Koman
June 1, 2009 @ 9:15 AMgovernment.zdnet.com/?p=4873Should the Supreme Court hear networks’ and movie studios’ plea to consider whether Cablevision’s remote DVR technology violates copyright law? The Justice Department urged no, Dow Jones reports. A federal appeals court said Cablevision could go forward with its plans to record, store and serve copyrighted content on its own servers instead of forcing customers to buy their own individual DVRs, rejecting the copyright industry’s argument that the scheme violates copyright law. Solicitor General Elena Kagan wrote in a brief that the court shouldn’t get involved. For the last 30 years, consumers have been able to record televised programs and to play back the recorded programming at a later time. Respondents’ proposed RS-DVR service is part of a broader transition from analog to digital recording and playback, and from business models where consumers purchase a tangible item to those where they pay for a service.
|
|
|
|
Post by towhom on Jun 13, 2009 6:01:51 GMT 4
20,000 sites hit with drive-by attack codeZDNet News & Blogs / Technology News
by Ryan Naraine
Posted: June 1st, 2009 @ 6:50 amblogs.zdnet.com/security/?p=3476&tag=nl.e589Hackers have broken into more than 20,000 legitimate Web sites to plant malicious code to be used in drive-by malware attacks. According to a warning from Websense Security Labs, the sites have been discovered to be injected with malicious JavaScript, obfuscated code that leads to an active exploit site. The company discovered that the active exploit site uses a name similar to the legitimate Google Analytics domain (google-analytics.com). This is unrelated to the Gumblar attack, Websense said. This mass injection attack does not seem related to Gumblar. The location of the injection, as well as the decoded code itself, seem to indicate a new, unrelated, mass injection campaign. The exploit site has been seeded with several different attacks targeted unpatched software vulnerabilities. The malware that gets loaded on compromised Windows machines is linked to scareware/rogueware (fake security applications). Malware purveyors have increasingly turned to legitimate Web sites to launch attacks, using SQL injection techniques to compromise and hijack high-traffic sites. According to data from MessageLabs, about 85 percent of Web sites blocked for hosting malicious content were ‘well-established’ domains that have been around for a year or more.
|
|
|
|
Post by towhom on Jun 13, 2009 6:09:45 GMT 4
U.S. Army servers breached by Turkish hackersZDNet News & Blogs / Technology News
Posted: Jun 01, 2009 4:44:56 AMnews.zdnet.com/2100-9595_22-307208.html?tag=nl.e589Hackers based in Turkey penetrated two US army web servers and redirected traffic from those websites to other pages, including one with anti-American and anti-Israeli messages, according to a report in InformationWeek. The hackers, who go by the group name 'm0sted', breached a server at the army's McAlester Ammunition Plant in Oklahoma on 26 January (2009) and a server at the US Army Corps of Engineers' Transatlantic Center in Winchester, Virginia, on 19 September, 2007, the report said. Investigators believe an SQL injection attack was used to exploit a vulnerability in Microsoft's SQL Server database in order to gain access to the servers. It is unclear whether any sensitive information was accessed, according to the report. Search warrants have been served on Microsoft, Yahoo, Google and other ISPs and email providers, while a criminal investigation is underway at the Defense Department, the US Army's Judge Advocate General's Office, and the Computer Emergency Response Team, InformationWeek reported. The same group defaced the United Nations website in 2007, also using a SQL injection attack. This article was originally posted on CNET News. Why did this take so long to hit the streets? Are you looking for more funding for an infrastructure overhaul. That is already a priority with the current administration. You have "stuff". You just want the game board set up in your favor, authorizing the use of a totally invasive "superstructure" to do what you are ALREADY DOING. Just like the previous administration's "legal manipulation" in setting up guidelines and protocols via the totally infamous "Patriot Act" and the enforcement by the "Dept. of Homeland Security" referencing data collection and monitoring of all communications without cause and without subpoenas. You've been doing this for YEARS - you finally got around to adding the "laws" authorizing these "procedures".
The concern I have is the introduction of AI platforms and programs (the "stuff") as cited in many articles, both in the open and on "the fringe" - like the one above.
There is no way I can accept that there aren't advancements already in place and in use with respects to AI applications - especially intuitive and self-correcting programs. Frankly, I think the only reason some of the research "trickles out" in main stream media is to add a layer of complacency for the general population and trip-wire some other research into cross-sharing so it can be tracked, squashed and/or incorporated into "non-acknowledged" tinkering.
Furthermore, it is a crying shame that this "not in the loop" attitude is alive and well...not even the POTUS is included. What a bunch of "goober-geeks"...
|
|
|
|
Post by towhom on Jun 13, 2009 11:01:08 GMT 4
HOW TO: Embed images in your postYou need an web image storage site. I use Photobucket. It's free (or you can upgrade for a higher storage quota and no ads). Here's the link:photobucket.com/You will be uploading images from your PC or MAC to your account, so you will have to save the image to your system first.
Photobucket includes general image editing options, like resize, crop, effects, etc. If you have an image editing program on your system (like Photoshop), you may want to edit and optimize for the web before you upload an image from your system for 2 reasons; 1) your picture size will be smaller so you will use less space from your account quota, and 2) high resolution images may force the use of the width scroll bar on a post page (this, however, can be done using the built-in image editors on Photobucket).
Set up your account as directed (the usual - user name, password, etc.).
Login to your account. It will automatically take you to your "album main page".
Locate the browse for image section: Click on browse button and select the image to upload from your system. Click on browse button and select the image to upload from your system.
Once you've found the image, click "Open" and the Photobucket page will display the file name. Name your image and click the upload button: Once it's uploaded you will automatically be directed to the page that allows you to add tags, descriptions, etc. These are optional. Once you're ready, click on the "return to album" button at the bottom of the page: Once it's uploaded you will automatically be directed to the page that allows you to add tags, descriptions, etc. These are optional. Once you're ready, click on the "return to album" button at the bottom of the page: At this point you can select to edit the image with the built-in image editors. Once that's done, you save the changes to the album or replace the original picture. You want to return to your album. At this point you can select to edit the image with the built-in image editors. Once that's done, you save the changes to the album or replace the original picture. You want to return to your album.
Now you want to select the image to post. Hover over the image and a semi-transparent drop-down box will appear below the image. You want to click on the option at the bottom "IMG code": I always right-click and copy (even though it will say "copied" once selected). I always right-click and copy (even though it will say "copied" once selected).
Go to your post message page on the site and "paste". You will see the following:< the html info for the copied link will appear here> (without the clarets) and in between the designations ![]() [/IMG] .If you hit the Preview button or alt+p, you should see the image displayed.
Hope this helps.
Sally Anne
|
|
|
|
Post by towhom on Jun 14, 2009 6:06:07 GMT 4
China's "Green Dam" Censorware Could Spawn a Zombie NetworkThe country's latest attempt to control its citizens' Internet use could backfire badlyTechnology Review / arXiv blog
Thursday, June 11, 2009
By Erica Naonewww.technologyreview.com/blog/editors/23654/Controversy erupted this week over reports that the Chinese government plans to require all computers sold in the country to come with software that screens for objectionable websites. Although initial criticism came from privacy advocates and those most concerned about censorship, experts have also now found that the software could introduce critical security risks to computers across the country. According to the BBC, the software communicates in plain text with central servers at its parent company. Not only does this potentially place personal information in the hands of eavesdroppers, but it could also allow hackers to take over PCs running the software, creating a massive zombie network that could deliver spam or attack other computers across the globe. [Note: Behold, the backdoor...]The report adds that the software does not seem to work as intended, sometimes blocking ordinary websites and failing to block others that contain objectionable content. And the software appears to work only on Microsoft Windows, not on Macs or Linux machines.[Note: This is not surprising. One point that should be made, however, is that a rather large number of servers in operation today utilize the Linux-based OS.]The news, while disturbing, is unsurprising. It's not the first time that attempts to censor and monitor users have placed personal information at risk. Late last year, for example, researchers at the Citizen Lab at the University of Toronto uncovered massive surveillance of users of instant-messaging service TOM-Skype, largely because the data being collected was unprotected and accessible over the Internet. The Internet does not lend itself to central control, and China's government continues to struggle with that fact, both on a philosophical level, as the larger debate on censorship shows, and on a technical level. [Note: The only thing ALL governments are "struggling with" is how to keep the general public and hackers from the "massive database archives" of information they already have - which is pretty much everything transported on all voice / data platforms. This does not take into account the "data" acquired via the "manual communications networks" (such as the USPS, UPS, FedEx, etc.) and surveillance networks.]
|
|
|
|
Post by towhom on Jun 15, 2009 3:45:55 GMT 4
Microsoft still has no patch for DirectShow hole Windows Secrets
By Brian Livingston
2009-06-11A flaw in Microsoft's DirectShow technology, allowing a hacker Web site to infect a visitor's PC, is a vulnerability that remains uncorrected in the Redmond company's Patch Tuesday updates this week. Fortunately, you can visit a Microsoft Knowledge Base article for a workaround that will close the hole, at the expense of disabling some QuickTime functionality. Use a one-button DirectShow fix or Registry edit Microsoft announced in its May 28 security advisory 971778 that a weakness in DirectShow was being actively exploited by some Web sites. The Redmond company revealed in a notice last week, however, that it would not have a patch ready for distribution by this month's Patch Tuesday on June 9. That means you're at risk if you open a hacked QuickTime file. According to Microsoft, the hole affects Windows 2000, XP, and Windows Server 2003 but doesn't affect Vista or Windows Server 2008. Because users of the vulnerable operating systems could be silently infected simply by visiting a bad Web site, I recommend that you put the workaround in place on all affected machines. Microsoft provides an easy "Fix it" button in KB article 971778. Clicking this button and installing the resulting hotfix closes the hole but also disables automatic parsing of QuickTime audio and video files. The article also describes a Registry edit that will accomplish the same end, but I see little reason to undertake manual editing when a one-button solution is available. The same article also includes a "reverse Fix it" button that will undo the workaround in case you desperately need to restore the broken QuickTime function. Iframe exploit requires tweaks for several apps Inserting infected code into legitimate Web sites seems to be a popular hacker tactic these days. Aside from the Gumblar family of attacks, which WS contributing editor Susan Bradley describes in today's Top Story (see article entitled "Big-name sites spread latest malware infections" below), a separate — but similar — line of attack involves HTML iframe insertions. An iframe is a rectangular area of a Web page that can contain text, images, or other content. According to a June 6 alert by Trend Micro researcher Roderick Ordoñez, hackers are using JavaScript to inject harmful iframes into unsuspecting, legitimate sites. The alert lists several applications that may be vulnerable to infection if you visit an infected site while older versions of the apps are installed: - Windows Explorer (Windows 2000, XP and Windows Server 2003)
- Apple QuickTime 7.1.3
- Microsoft ActiveX control wzfileview.fileviewctrl.61
- Microsoft Data Access Components (MDAC)
- Internet Explorer 7
Trend Micro links to a fix — or at least a description of the problem — for each of the above applications. For more info, please read Ordoñez's alert.
|
|
|
|
Post by towhom on Jun 15, 2009 6:33:51 GMT 4
Big-name sites spread latest malware infections Windows Secrets
By Susan Bradley
2009-06-11Going by such names as Gumblar, JSRedir-R, Martuz, and Beladin, a new generation of malware has managed to surreptitiously place malicious JavaScript code on tens of thousands of popular Web sites. The hacker scripts try to infect site visitors and then attempt to use their compromised PCs to spread the infection to yet other sites. Over the past month, the security services ScanSafe and Sophos have reported infections on such major Web sites as ColdwellBanker.com, Variety.com, and Tennis.com. Niels Provos reported in the Google security blog on June 3 that sites infected with Gumblar numbered about 60,000. Visitors became susceptible to infection simply by opening the sites in Internet Explorer. After the script infects a PC, it attempts to spread its code to any Web site accessible via that machine's FTP client, if one is present. Webmasters often use FTP to make changes to the sites they manage. If FTP software is configured to save a webmaster's sign-in information, the malware can edit itself into a Web site's pages. Once a PC is running this class of malware, the hacker code tries to trick the user into opening infected PDF and Flash files. If the PC has an unpatched version of Adobe Reader, Acrobat, or Flash, opening an infected file can install a keylogger or other malware. In the case of Gumblar, Google search results in an Internet Explorer window are rewritten — in a way that end users may not notice — so the links point to hacker sites laden with infected PDF and Flash. Security firms have made efforts to block domains that serve as malware destinations in this latest round of attacks. But the bad guys quickly move to substitute other domains in what has been compared to a game of Whack-a-Mole. Meanwhile, it's not so easy to shut down a well-known, legitimate site that's infected (although many such sites have quickly been cleaned up). You can't protect yourself simply by visiting only "trusted" sites, because there's no easy way for an end user to determine whether a legitimate site is infected. Fortunately, you can stack the odds in your favor by following the guidelines in the Windows Secrets Security Baseline: - Step 1: Use a hardware firewall.
- Step 2: Install a set of security software.
- Step 3: Scan your system regularly with a software-update service (more on these below).
- Step 4: Use Mozilla's Firefox or Google's Chrome browser, both of which are more secure than Internet Explorer.
The rise of a new form of Web-based threat On May 27, the Microsoft Malware Protection Center blog reported that a malware family Microsoft refers to as Gamburl and Redir was infecting legitimate Web sites by embedding malicious scripts in the sites' HTML code. A system running Windows XP could become infected simply by opening a seemingly trustworthy site. (Gumblar, also called JSRedir-R and Martuz, doesn't affect Vista PCs, according to the Unmask Parasites blog.) Once an XP machine is infected, passwords for FTP sites are retrieved and placed into a file called sqlsodbc.chm. This file is a legitimate SQL help file in Windows XP and 2000, but it's not used on Vista machines. To determine whether Gumblar has struck your PC, test sqlsodbc.chm, which is located in XP's C:\Windows\System32 folder: - Step 1. Download the free FileAlyzer program from the Softpedia site and install the program on your system.
- Step 2. Press the Windows key and E to open an Explorer window. Navigate to the C:\Windows\System32 folder, right-click the sqlsodbc.chm file, choose Analyze file with FileAlyzer 2, and note the file size and SHA1 hash value. (See Figure 1.)
Figure 1. The FileAlyzer utility checks the sqlsodbc.chm file to determine whether your PC is infected with Gumblar.
- Step 3. Compare the file size and SHA1 hash value with the listing of good file types published on the Microsoft Malware Protection Center blog. If the file doesn't check out, update your machine's anti-malware software and run a full system scan. The scan should find and clean out the infection. On my test PC, the sqlsodbc.chm file had the expected values, which proved that the system wasn't infected.
Once your copy of sqlsodbc.chm comes up clean, you need to take steps to ensure that it stays that way. Download the latest virus definitions for your antivirus software. Also, ensure that Adobe Reader, Acrobat, Flash Player, and all your other third-party media players and applications have the latest patches. Home and small-business users can run a free update checker such as Shavlik Patch, which you can download from the vendor's site. (Note that the program requires the free Google Desktop, which is available on Google's site.) A complete review of Shavlik Patch and several competing update programs is in my May 28 top story. [Note from towhom: This is in my paid subscription portion of the newsletter. Due to that, I will not post the story. Windows Secrets donates more than half of the proceeds from their newsletter subscriptions to the support of children around the world. There is no set price. Donate what you can afford.]For business networks, I recommend Shavlik's NetChk Protect. I use this utility — which costs from U.S. $104 for two seats — to patch my own firm's network. You can find information about NetChk Protect on Shavlik's site. For an added measure of protection, configure your PC to use the OpenDNS service, which lets you block categories of sites that you don't visit. You'll find complete instructions for making the required changes to your router on the OpenDNS tutorial page. To make OpenDNS your DNS server, you can run your router's advanced settings program and manually set its DNS options to 208.67.222.222 and 208.67.220.220. (See Figure 2.)  Figure 2. Make OpenDNS your primary and secondary DNS server in your router's DNS settings to block potentially dangerous sites. Figure 2. Make OpenDNS your primary and secondary DNS server in your router's DNS settings to block potentially dangerous sites.It's theoretically possible to manually enter in the OpenDNS settings page the URLs of sites you want to block. But trying to keep up with the latest list of Gumblar sites is nearly impossible. ScanSafe's STAT Blog indicates that the rate of Gumblar infection is slowing. But new infected domains — all of which use China's .cn top-level domain — are popping up as fast as others are being shut down. Boost XP's defenses against Gumblar-like attacks If you feel your XP system needs more protection — for example, you own a PC used by unsupervised teenagers — consider creating user accounts that lack administrator privileges. Granted, XP's limited accounts are often a pain to use because they restrict downloads, settings changes, and other common actions. An article on Microsoft's site explains limited user accounts and describes how to set them up. [Note from towhom: I highly recommend establishing and using a limited user account for general web browsing and software program access. If you know you are going to be downloading programs or need to work in an administrative capacity on your system, then log out of the limited user account and log in as the administrator account. Yes, this can be a hassle, however, it is another layer of protection for your system.]Fortunately, the type of limited accounts in the forthcoming Windows 7 will be much easier to use. This is because the most common applications will run properly under Win7 without administrator rights. Steve Friedl's Unixwiz.net site includes a Tech Tip that describes Windows 7's enhanced User Account Control. Gumblar definitely makes Web surfing with Internet Explorer more hazardous. If your PC is infected, merely searching in Google for seemingly innocent topics can lead you to a site you never intended to visit. Google's Niels Provos recommends in his Top 10 Malware Sites blog that people use Firefox, Chrome, or another browser that taps into Google's Safe Browsing API. The API blocks Web destinations on Google's list of potentially dangerous sites, which the company claims to update continuously. Here are some additional ways you can protect yourself: - Make a full system backup. Create a backup of your PC using drive-imaging software such as the $50 Acronis True Image Home. (A 15-day free trial can be downloaded from the Acronis site.) Be ready to roll back to a prior image should your PC become infected.
- Use Windows SteadyState. This free program "freezes" a machine, preventing changes that could be harmful. For more information and a download link, visit the product page on Microsoft's site. (Windows Genuine Advantage validation is required for the download.)
- Browse in a sandbox. WS senior editor Ian "Gizmo" Richards described free sandbox programs in an Oct. 16, 2008, article. A sandbox lets you open suspicious links without putting your system's security at risk.
- Don't use Internet Explorer. All versions of IE are vulnerable to Gumblar and similar Web threats, but especially IE 6 is an infection waiting to happen. If a site or application requires Internet Explorer, update to IE 8 if you can. If you can't, download IE 7 as a bare minimum (although it's by no means a remedy). You can download IE 7 from Microsoft's Download Center and IE 8 from the browser's page on Microsoft's site.
If you simply must use IE 6 because some site or application requires it, urge the errant developers to make their code support the latest version of IE instead.
For tips on running and optimizing Firefox, Chrome, and other non-IE browsers — including OpenDNS and the security-enhancing NoScript extension for Firefox — see a comprehensive six-part article at MaximumPC.com.
[Note from towhom: This is an excellent article with great tips for a variety of operating systems.]
Some of the above precautions may sound like paranoia, but I consider them the digital equivalent of locking your car doors and staying out of dark alleys.
|
|